So you just found out how big tech and government agencies are using your data and trying to sell you stuff that you probably won’t ever need. You have decided that you want to have enhanced internet privacy and sufficient data security. Where do you start?
Well, you start with Tor. Tor takes care of all the problems we have mentioned above.
Tor is an essential piece of software for anyone who wants to have more anonymity on the internet. Tor actually started as a project and is still one. The team behind it offers a number of products, all of which come with the Tor brand name.

Since you want to have privacy while you browse the internet, you need the Tor browser. Tor browser has made a name for itself in the community of privacy-conscious internet users by offering encryption that works and covering up the tracks they leave behind while surfing the internet.
How Does Tor Really Work?
In the middle of the 1990s, a new technology emerged due to research projects carried out by a couple of computer scientists and mathematicians. That piece of technology was labeled as onion routing. At the time, onion routing introduced something new to the world of privacy. It used layers of privacy to provide anonymity to internet traffic.
Fast forward to the 21st century, the Onion Router Project came to be known as Tor. It was also around this time that the online community was able to get its hands on Tor and participate in anonymous web browsing. Tor made use of a vast number of users connected to the same network to provide an increasing amount of anonymity. The strength of Tor was the number of users who were willing to contribute to the network by acting as nodes.

If we jump forward to today, Tor is the biggest anonymous network in the world which consists of nodes or users numbering in the thousands. These ‘nodes’ live in various parts of the world, but all help to create the Tor network and provide security to any user’s traffic.
An easier way to think about Tor is to think of it as a network that takes advantage of the internet and a special internet browser to give you an added layer of privacy on the internet.
The Tor browser essentially strips the user’s internet traffic of any information that may identify the user in any way. Then it routes that traffic via the Tor Network. In the Tor network, the user’s internet traffic goes from one node to another (and it keeps going from one to the other to further anonymize the traffic). This is how Tor encrypts the user’s traffic and personal data.
Because of these different layers of protection, Tor is likened to an onion that also has layers upon layers of protection for its core.
Once a given user’s traffic has gone through a sufficient number of nodes, it exits the Tor network via an exit node. Only then does the user’s internet traffic sees the light of the open internet.
If you are not Edward Snowden, the Tor network gives you perfect security as far as tracking is concerned since there is no way to know where it came from.
Any website that you try to visit from the Tor Browser will have no idea where you are on the map since your traffic exited the Tor network from an exit node located in any part of the world.
Do I only Need a Tor Browser To Use Tor?
For the most part, yes.
Here are the steps you need to take.
How to Install The Tor Browser On Windows
Step 1: Go to The Official Website of Tor

The link you are looking for is https://www.torproject.org/download/.
Step 2: Download The Tor Browser For Your Platform

All that means is that you need to make sure you download the version meant for your operating system. Download the file for Windows if you are using Microsoft Windows as your primary operating system and change your option if you are on macOS or Linux.
Step 3: Execute The Downloaded File
Once you download the right Tor browser file on your system, you need to navigate to the place where you saved it and then double-click on the downloaded file. When done correctly, it should launch the installation wizard.
The installation wizard itself is pretty straightforward to go through. Generally, though, you will only need to click on the Next button until the Installation wizard completes itself.
If you have ever installed any other program on your operating system this step should be a piece of cake for you.
Step 4: Launch Tor
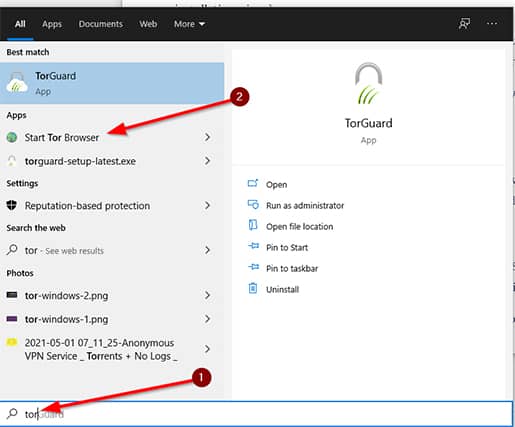
This should be easy enough. Double click the icon for the Tor browser if it is on your desktop or search for it using your operating system’s search function to find it and then launch it.
Step 5: Configure Tor
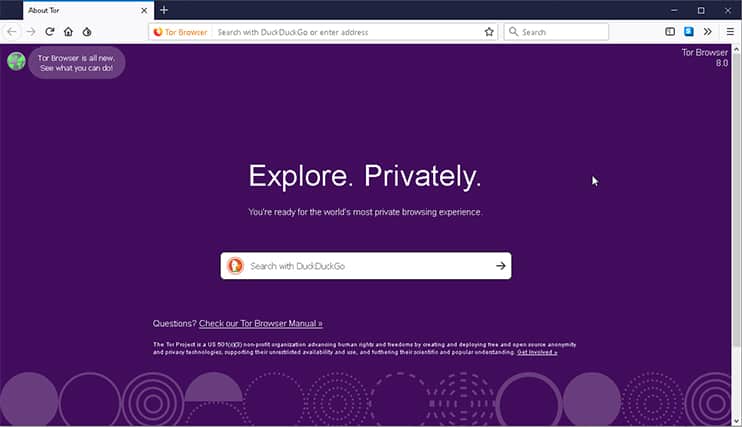
This is where you might have to perform a couple of extra clicks. Since Tor isn’t your run-of-the-mill web browser, it will ask you to configure some settings the first time you launch it.
Of course, you can skip that part and ask the browser to connect to the internet. But you should think about going for the other option (which is to configure the browser) if you live in a country with a restrictive government.
Traditionally these countries are thought to be China, Iran, and/or North Korea.
But even if you skip this part and hit Connect, your Tor Browser will still take a minute or two to calculate and reserve a set of exit nodes or relays via which it will protect your connection and internet traffic.
Once you are done with that part, then the Tor Browser works exactly like any other mainstream web browser. You can go to any website and not have it record your data and target you to hyper-specific ads.
The Tor Browser may ask you to check the security settings on your browser from time to time. Now, you can ignore that message. But if you want the Tor Browser to be at its best while working for you, you need to make sure all the settings remain in their default states.
Now, because the Tor Browser has to move your internet traffic through a number of nodes before it can reach its final destination and then get back to your machine, you will experience a slower internet connection speed.
If it gets out of control, though (meaning the websites you want to visit are not loading fast enough), you can tweak Tor settings to rectify the problem. The Tor Browser allows users to check for a different connection path which might offer better speeds.
To get to the correct settings, you need to,
Step 6: Click the Menu icon
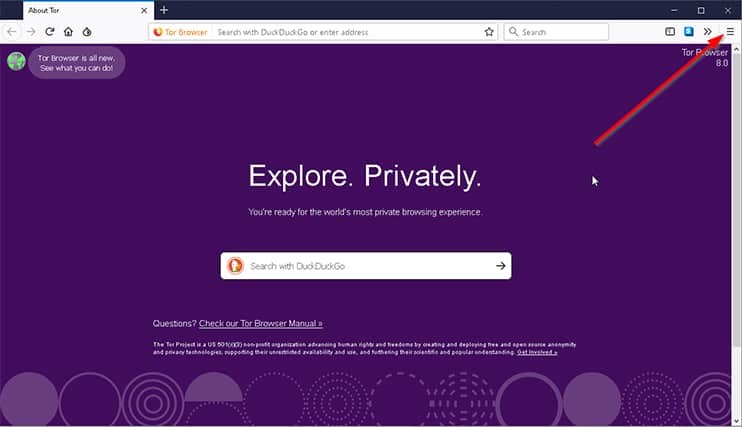
The icon we’re talking about here is the one that comes in the shape of three horizontal lines on top of each other in the top right corner of the screen.
Step 7: Click on New Tor Circuit For This Site
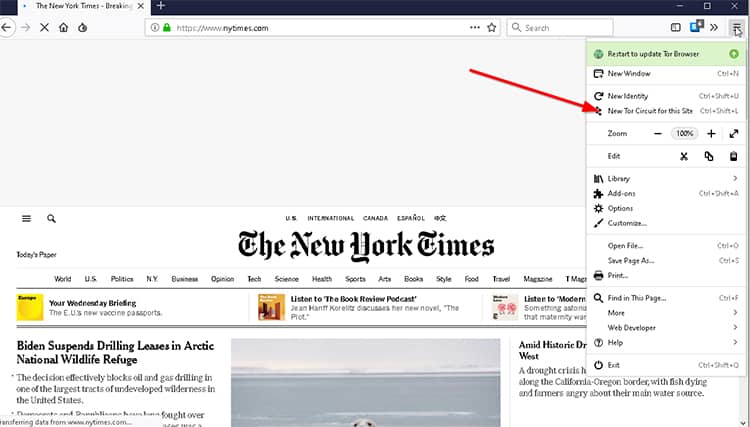
When you click on the menu icon, you should see an option labeled New Tor Circuit For This Site in the sub-menu. Click it, and the Tor Browser will find a new circuit for you and then connect you to it.
Whether or not it improves your browsing experience is something you’ll have to see for yourself as the option doesn’t guarantee that it will always increase browsing speed.
How to Install The Tor Browser on Linux (Manjaro)
Installing applications on a Linux platform is different from Windows in the sense that there are so many flavors of Linux and so many different ways of installing the same application.
For example, if you are using Manjaro, you only have to take the following steps to benefit from what the Tor browser offers.
Step 1: Click on The Green Button in The Bottom Left Corner of The Screen

Step 2: Type ‘Software’ Without The Quotes

Step 3: Search For The Tor Browser Bundle
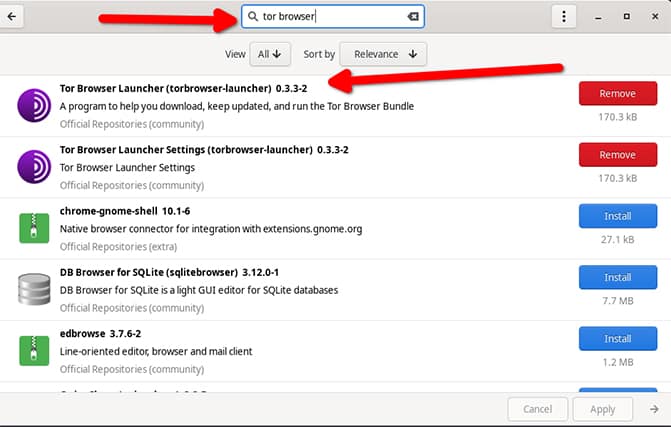
Step 4: Click on The Tor Browser And Install it

Depending on your settings, Manjaro may ask you for your password.
After installation is finished, you can protect your non-Tor IP address and network traffic (every data packet) by launching the Tor service browser instead of your regular web browser and thus become a Tor user.
Now you may not be using Manjaro. In that case, you should follow the steps given below. These will work for most Linux distributions.
How to Install The Tor Browser on Any Linux
Step 1: Go to the Official Website of Tor
As mentioned before, the link for that is www.torproject.org/download/.
Step 2: Download The Right Linux File For Your Machine
Mostly, your download file will come in the shape of a .tar.xz file.
Step 3: For More Security, Verify the Signature Associated With the Download
Step 4: Go to the Place Where Your Linux OS Stores Downloaded Files
Most of the time, this will be in your home directory inside the Downloads folder.
In any case, once you find it, you need to perform a right-click on it.
From there, you should click the option that says Extract Here.
Step 5: Access The Tor Browser Folder
This should come about as a result of you extracting the downloaded file.
Perform a right-click on the option that says start-tor-browser.desktop. Then you need to click on Properties. Or, depending on the version of your Linux operating system, you may see the option that says Preferences.
When that is done, you need to click the option that says Execute. It is a good idea to check Allow Executing File As Program as well since we are trying to run a script in the shell.
Step 6: Click The Tor Browser Symbol To Launch
This is the final step.
How to Uninstall The Tor Browser
Getting rid of the Tor Browser is not hard, especially if your machine is running Linux and/or Windows.
All you have to do is delete the folder containing The Tor Browser, and you are done.
Of course, if you want to do it cleanly, you should go the proper route, Start Menu > Control Panel > Uninstall Program > Select Tor Browser From The List.
For Linux, a lot will depend on the distribution you are using. Manjaro makes it very easy where you have to go to Start Menu > Software > Search For The Tor Browser > Click Remove
For macOS users, the manual process of deleting The Tor Browser remains the same. However, you are free to use a third-party application that you trust.
Can you be tracked on Tor?

In some scenarios, yes. Someone may be able to track you even when you are using Tor. Let’s see how.
You see, even though the Tor Browser itself is perfectly safe, the things you do on it are not. For example, the default settings on the Tor Browser ensure no website is able to run Javascript. The Tor browser also disables plug-ins for more security. Moreover, the browser will always put out a warning message before it takes you to another application that may compromise your privacy.
We don’t mean to say that Javascript is a definite security risk. It is not. But for people who want that extra layer of security on the internet, they should keep Javascript turned off as some websites can use Javascript to know your real IP address.
The same goes for Adobe Flash as well. If a video player application wanted to, it could compromise your IP address and send it to a third-party service.
You have to be very careful on the internet if you want maximum privacy. However, as mentioned earlier as well, if you do not change the default settings of Tor, you can avoid most of these problems.
Is using Tor safe?

In short, yes. Using Tor to surf the internet is very safe. It is probably the safest way to surf the internet if you want a plug-and-play solution to private browsing.
However, as mentioned throughout this post, you need to take care of some caveats.
Mostly, hackers and other bad actors can use scripts present on Tor to exploit users and steal their information. In this regard, your internet service provider is not much better either. It can tell if you are using Tor.
That is why some Tor users like to use a VPN over Tor to be perfectly safe. We have already mentioned that if a group like the NSA is after you, there isn’t much Tor can do. Such groups can control relays or nodes on the Tor Network and follow users. This also holds for online technology companies like Facebook and/or Google, who have shown time and time again to have highly sophisticated methods of tracking users online.
If you want to make Tor as safe as possible, make sure you do not connect to a website or a service that does not offer an HTTP connection. Once your data leaves the Tor network, it doesn’t have encryption protection, and unencrypted data traveling throughout the broader world of the web is never good news for your privacy.
Finally, avoid using the BitTorrent client over Tor if you are serious about not letting anyone see your original IP address.
Is Tor really anonymous?

Yes, Tor is anonymous as far as the common internet user is concerned. But if you are pointing towards some theories that say the CIA or the FBI has a backdoor connection to Tor, then that is something no one can confirm or dismiss at the moment.
We’ve talked about how the Tor browser can give rise to speed issues because of the fact that it is a volunteer-run network. Readers need to understand that no piece of software offers perfect privacy or anonymity in any situation.
Of course, we’re not saying that Tor doesn’t work. Far from it. What we are saying is that Tor has some limitations that can become risks if you know nothing about them.
At this point, you already know that the Tor network consists of Exit Nodes. The Tor browser routes your traffic through the network with the help of these nodes, which are selected at random. Because of that, websites/apps/services can’t tell which computer actually made the request once your traffic does reach its final destination.
The finer point to note here is that your traffic has to leave the Tor network to actually get to where it is supposed to go. Let’s understand that better with the help of an example.
Let’s assume you want to visit Google but want to do so privately. So you do what any privacy-conscious person would do. You download the Tor Browser, and you go to www.google.com.

In such a scenario, the Tor Browser will (as we have mentioned before as well) will encrypt your internet traffic and then pass it through a predetermined number of exit nodes or relays. Eventually, though, the traffic will have to leave the Tor network and then go to Google servers and then connect to them.
It shouldn’t be hard to understand that, in this case, Google knows the IP address of the last exit node and can monitor the internet traffic once it enters the open internet. In even simpler terms, the traffic is unencrypted once it leaves the Tor network and remains so the rest of the way.
That isn’t as bad for privacy as it used to be since the vast majority of popular websites use HTTPS, which encrypts the user’s connection. If you are accessing any Google services, you are pretty much safe because all of their websites use HTTPS.
So now, the problem becomes the exit node since the exit node knows that the traffic it just let pass through it connected to a Google service. Change to a website that does not use encryption, the exit note has all the opportunity in the world to record your internet activity and then keep its tabs on you as you visit other websites and services on the internet, search for stuff online, and communicate with your loved ones.
It is also true that you can’t really do anything about the exit node and you can’t use the Tor network without one. In other words, you essentially give consent to using an exit node when using Tor. We mentioned beforehand that the Tor network is a volunteer-run network and for simplification, you can imagine each node, including an exit node, as a computer that belongs to a person.
The exit node is different from a normal relay or node in the sense that the person running the exit node has to provide consent to becoming one for legal reasons. It wouldn’t be a far-fetched idea that government agencies would have caught onto that and would have set up some tor exit nodes on the Tor Network.

Using the exit node, they could monitor all tor traffic that leaves the network and then use that information to do all types of good for society, such as catching criminals and stopping misinformation. They could also use the same setup to punish people like Edward Snowden or anyone who makes the mistake of speaking up for his/her rights or exposes corruption in government departments.
Security researchers showed that one could intercept passwords and email addresses and the related messages sent via the Tor network if they ran an exit node the right way. That happened about 15 years ago. But even there, users made the mistake of using services that did not offer encryption or HTTPS connections.
We should reiterate here that Tor only encrypts your internet traffic for the duration of its passage through the Tor network. Once it leaves the Tor network, Tor can’t do anything to protect that traffic.
To guard against this problem, you must never use a service or a website that does not offer an HTTPS connection when using the Tor Browser.
Keep in mind that government agencies are not the only actors that can sign up for a Tor exit node. Hackers and other cybercriminals can do that as well.
Can police track Tor?

An even more specific question that may be coming to your mind is:
Can police track your internet activity even if you are using Tor?
The answer is not that clear. So first, we’ll say yes. And then we’ll say no. Allow us to explain.
Let’s say you are going through an airport or any highly-secured facility and a team of law enforcement agents decide to check your laptop. If they do a forensic analysis of the machine, they can potentially know whether or not you used Tor and what you did in the online world when you were using Tor.
You may be able to remedy this problem by using an extra-private operating system such as Tails. But other than that, they will know where you went while using Tor.
Another case is where law enforcement agencies are able to install spyware on your laptop. Then too, even if you use Tor, the police can track you and monitor what you did online.
The above two methods are not the only ones law enforcement agencies use to monitor potential criminals on Tor. The police now have the ability to control Tor websites.
In fact, they can control any website they want, provided they get the clearance for it. Once they have control of the website, they can inject malicious code into it with the help of common programming languages such as JavaScript. And that is all they really need to do to know your online identity.
With that out of the way, if you connect to Tor the usual way and you are not a highly sought-after criminal, then no one can know what you are doing online. As far as the websites that you visit while using Tor, the police can’t know anything about it. Your internet service provider has to remain out of the picture as well since it doesn’t have the necessary technologies to go past Tor defenses.
As mentioned in this section, the situation will change dramatically if you run into a website that the police itself owns and has the personnel available to run different exploits.
This is where you need to check if the Tor Browser has disabled Javascript for you. We have heard that on computers, Tor Browser doesn’t automatically disable Javascript.
The Disadvantage of Using Tor

We’ll start with the obvious one.
Tor will slow down your internet connection. Since all of your internet data has to move from one node to the other before making it to the landing place, it takes more time for you to receive a response.
Pretty much every privacy product will slow down your internet connection speed.
Of course, if you think about it, whether or not the Tor Browser is slow shouldn’t matter to you if you know what type of activity is best to carry out over Tor. For example, you should try to avoid downloading or streaming stuff while on Tor.
If you think Tor will provide you with some security while you torrent then think again. Tor Browser may be able to hide your torrenting activity but the act of torrenting may give away your data and/or IP address since you have to connect to a swarm that consists of other people.
Another problem with using Tor is that you become stand out from the crowd. Again, Tor will hide your activity. But your internet service provider might find that interesting and may suspect you for something untoward. If some law enforcement agency asks your ISP to note down people who are using Tor, it will probably oblige depending on the laws in your country.
And once government agents know that you are using Tor, they might try to surveil your internet usage.
The final disadvantage we want to talk about here is not a disadvantage but a misconception. A lot of people who start out with the Tor Browser seem to forget that in the end, the Tor Browser is just a web browser. It can provide protection to your data by encrypting it and passing it through the Tor network, but as far as your other traffic is concerned, it can’t do much.
You can certainly use only The Tor Browser to do everything on the internet. But for most of us, that is not the case. So any other app that you use for any purpose whatsoever, will not have Tor protection since you are not using the Tor Browser.
That is the reason why a lot of users who install the Tor also use a VPN. In fact, the combination has caught on with the privacy community enough to have its own term called VPN over Tor.
Conclusion: Tor Users Should Keep Using Tor Project Browser to Access Tor Network

The Tor client is a fantastic tool to enhance your privacy on the internet. It allows (Tor) users to not only surf the ‘normal’ web (like a normal web browser does) but also the deep web or the dark web.
As good a tool it is, Tor is far from perfect. Under the right circumstances (mainly some entity monitoring exit tor nodes or any active tor relay nodes for that matter), your internet service providers can probably tell if you are using Tor (no one has currently managed to block Tor though). Using a VPN with Tor will help you fix that problem and limit what anyone can know about anything you do on the internet by studying your web traffic via various traffic analysis techniques.
If you live in a place like the US, using Tor and a VPN has become more important than ever since recent law changes now mean that internet service providers have the legal clearance to collect user data.
For those who can’t afford Tor over VPN, just Tor or just a VPN service.
Advertisers and third-party marketing companies are not going to stop collecting data since they are not doing anything illegal. They may be engaging in a lot of unethical stuff, such as infringing a user’s right to privacy, but that is a topic for another day.
For now, you can protect yourself (and any number of IP addresses) from all the data collection programs out there with a simple browser called Tor Browser.
People who do not have the patience to understand how the Tor browser constructs the Tor network (as mentioned before, in brief, it uses middle relay nodes, exit relay or nodes, other active Tor relays or Tor node to an anonymous network) but would still like to surf the web anonymously (and not generate a browsing history page) without using a ton of browser plugins, they should look at other web browser apps such as Brave and Epic.
